BYOD (Bring Your Own Devices) has become increasingly popular in the modern workplace, but such policies open the door for security breaches.
The exponential rise of BYOD policies in the business world has revolutionized the face of IT security, forcing many enterprises to rework their network management strategies entirely, in order to safeguard sensitive information against potential breaches.
The possible threats posed by the implementation of a BYOD initiative are not all immediately obvious, and many organizations do not realize the need for increased protections until a problem arises. Whether you already have a BYOD policy in your place of work, or you’re considering the introduction of one, it is important to know the risks, and be aware of the steps you can take to protect yourself and company interests.
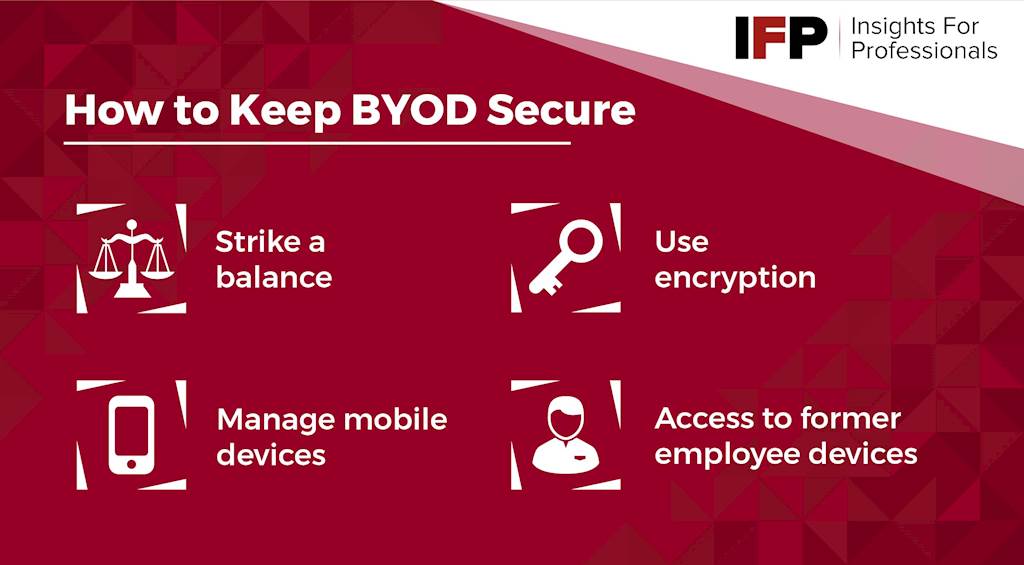
Striking a BYOD balance
While concerns surrounding the security issues associated with BYOD policies are widespread, many businesses neglect to tighten up their systems sufficiently. This is often because the introduction of multi-layered security is seen as a barrier to the inherent flexibility of BYOD. In other cases, companies simply assume their existing security is sufficient, without realizing the extent of risks posed by opening up a network to personal devices.
However, this does not need to be the case, as a truly comprehensive security strategy is one that accounts for the worst case scenario. What this means is that if your frontline security fails, your interests are still protected. One of the first steps you can take is to encrypt sensitive data, and ensure that access to decryption keys is strictly limited to those who require it.
Encryption is key
You can, and should, implement encryption protocols at multiple levels. In addition to encrypting the data itself, device level encryption is essential on all devices with access to your network or files. Most modern phones and tablets have built-in encryption, protecting data behind a pin, password or fingerprint scanner. This prevents data being downloaded onto another system while the device remains locked. Ideally, devices should use multi-factor authentication (MFA) where possible.
Finally, you should also consider your network encryption. This protects data from interception and theft while in transit, by preventing unauthorized access to the network. Unfortunately, not all websites and applications use secure data transmission channels, and can become a backdoor into your device for hackers and malware.
Mobile Device Management
Not all security breaches are the result of malice. Unfortunately, it is all too easy for an employee to inadvertently expose your business to external threats. This can occur through something as simple as signing into an unsecured WiFi network, or accepting permissions on an app without understanding the full implications. For example, if an app asks for full access to a user’s Google account, this could include all of their private data, which may include business emails and documents if this account is also used professionally.
When introducing a BYOD policy, you will need to ensure all users are made aware of the potential risks, and how to avoid them. Draw up a comprehensive contract, detailing company policy on the use of BYOD devices. This should include a list of accepted applications, as well as an outline of protocols for handling negligence, and reporting potential breaches.
Former employees
Careful management of BYOD employees who later leave the company is also vital. You need to know that all company information, and access has been removed from the device. A common policy is to cover this eventuality in user contracts. Some BYOD schemes require users to completely wipe their device if they leave the company. Others include clauses permitting the employer to request a wipe at any time, should security concerns arise.
Even then, there is the risk that an employee may have made external copies. But while you cannot necessarily prevent this from happening, you can still include a clause legally obligating them to destroy all such information following the termination of their employment.
The idea of having their device wiped is unpopular with many individuals. However, at your discretion, you may deem it sufficient for employees to demonstrate that they have wiped all relevant applications and files. On the other hand, you are also within your rights to point out that the policy is an essential security requirement of participating in the BYOD scheme. Your business security is important, and you should not feel obliged to compromise it.
Is there no other way?
While all of these risks are serious matters, that does not mean you should be discouraged from exploring the potential of BYOD scheme in your workplace. If you implement a thorough and comprehensive policy, and take steps to safeguard against the risks described above, you can enjoy all the benefits of a mobile workforce, while remaining in full control of your assets and sensitive data.
CYOD
However, there are other options which may be more suitable for your business, or afford greater peace of mind in terms of security. The first alternative is CYOD (Choose Your Own Device). This functions similarly to BYOD, except that the employer provides a list of suitable, approved devices from which employees can use. The device can then be preloaded with the necessary applications and security measures.
The downside is that this affords less freedom to your employees, and may mean some members of your team have to select devices they are less familiar and comfortable with. This can also lead to some employees being less productive, and more likely to run into technical issues while adapting to the new device. In addition, your business will be responsible for the management of invoices for all devices on a CYOD scheme.
COPE
The other option is COPE (Corporate Owned Personally Enabled). Under this scheme, employees choose their device, and a plan that suits their needs, which is usually subsidized via agreement between the employer and the carrier. Your business can then equip the device with the required security and applications, much like CYOD.
The user then has control over the device, invoice management, and their choice of plan. However, the device essentially belongs to the company. The primary benefit of this is that it makes it easier to enforce data protection policies in cases where an employee leaves the company.
If the shoe fits
The final point to bear in mind when weighing up these options is that they are not mutually exclusive. You may find it suits your business model to have some team members on a CYOD scheme, while others use BYOD or COPE, depending on their role, access privileges, or individual needs. All three options are subject to exploitation through human error and exposure to unsecured networks, so a multi-layered security management system will still need to be implemented, whichever option you choose.
You may also need to upgrade your network capacity to enable BYOD, ensuring that it is able to handle the strain of being accessed by numerous devices. An outdated system can be slow, and subject to crashes, reducing productivity, and putting unnecessary pressure on your IT team.
Ultimately, a sophisticated IT security strategy is essential even without allowing the use of personal devices. If you decide BYOD is not suitable, the measures described above can can still assist in reinforcing the overall security of your business. Furthermore, if you change your mind in the future, or decide to embrace COPE or CYOD as an alternative, you will already have the foundations in place for a smooth introduction of new policies.
Access the latest business knowledge in IT
Get Access






Comments
Join the conversation...