In fact, in the first quarter of 2017, Kaspersky Lab detected 1,333,605 malicious installation packages, which is almost as many as in the 4th quarter of 2016. The report also found that in Q1 2017, there were 218,625 ransomware installation packages detected on mobile devices – which is 3.5 times more than in the previous quarter.
The business sector has become a hot target for ransomware over the past years. When a business does not have the necessary mobile security tools and policies in place, they could easily fall victim to ransomware. Such attack could lead to negative consequences such as permanent loss of sensitive data, disruption to regular operations, financial losses incurred to restore systems and files, and potential harm to an organization’s reputation.
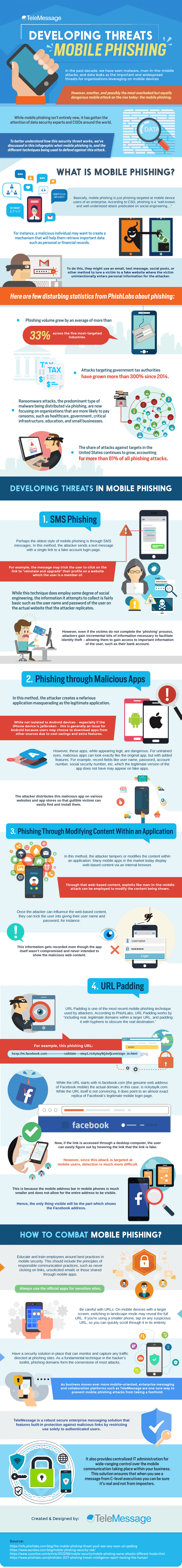
These figures only prove that companies allowing the use of the mobile device in their business must take mobile security more seriously than ever. Aside from ransomware, cybercriminals are also using another technique to steal critical information from companies through a mobile device – phishing. To learn more what mobile phishing is and what businesses can do to minimize their exposure to this threat, check out this infographic from TeleMessage.
Access the latest business knowledge in IT
Get Access




Comments
Join the conversation...